There’s been a lot of buzz this week about a USA Today reporter who was hacked by another passenger onboard an American Airlines flight recently:
“I hacked your email on the plane and read everything you sent and received. I did it to most people on the flight.”
He had verbatim detail of a long email that he repeated back to me essentially word for word.
We’ve received tons of questions asking if it’s safe to connect to airplane WiFi in light of this, and I figure it’s something others are wondering about as well.
No public internet connection is inherently safe.
Whenever you’re using a public connection you’re exposed to flaws in the network, and are a bit at the mercy of anyone using that same network. It doesn’t really matter whether you’re at a coffee shop, a hotel, or on an airplane.
To protect your data, an easy option is to use a Virtual Private Network (VPN). These are inexpensive, easy to use, and truly — there’s no reason not to.
How do VPNs work?
Alright, so the disclaimer here is that while I am tech-y for OMAAT, I am not a computer engineer or anything. My husband, who is a computer engineer, gave a pass to this explanation with an “Ugh. That’s really simplistic, but more or less accurate” followed by an “It’s really not appropriate to turn this into an extended sex metaphor, you should edit that part.“
So this is a basic for-my-mom explanation. 😉
When you connect to the internet, your communication with various websites is either encrypted or open based on what site you’re visiting.
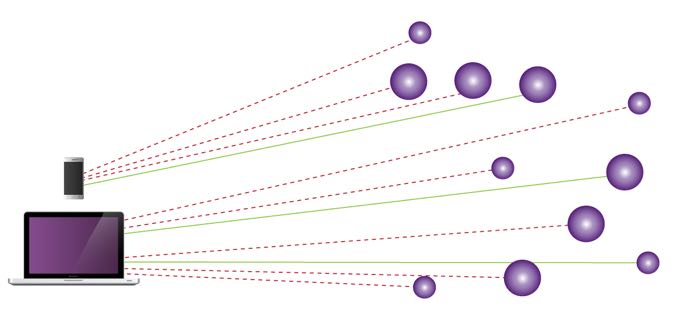
Things like Gmail, your bank, Facebook — those are always encrypted (that’s what the https means at the beginning of the URL). So in theory those should be safe, but you’re relying upon the destination site and your internet service provider (ISP) to keep that connection secure. If you’re at home, you can probably trust your own network, but even https can potentially be circumvented by the ISP forcing you to use an alternate certificate (that’s why you sometimes see that padlock with the slash through it in the navigation bar, because the site certificate is suspect).
It gets complicated, but the takeaway is that even normally encrypted sites aren’t necessarily secure when you’re accessing them from a public network.
And everything else is potentially open-season.
Once you’re using a VPN, everything is encrypted to the server of the VPN provider. So it doesn’t matter as much what the security level of the individual sites is, because your VPN creates a shield for your device.
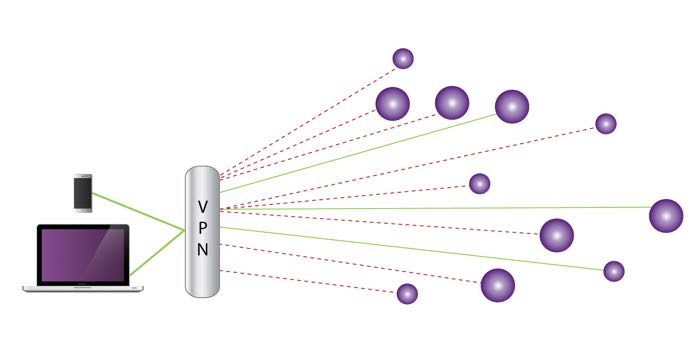
The VPN shield protects you from people reading your data when on public or shared WiFi (whether it’s Starbucks or Gogo). It also prevents less-legitimate sources from looking at your data (be it the guy hacking from the row behind you or the Chinese government), because all they can effectively see is the connection to the VPN. The rest of your internet usage goes into an opaque tunnel.
While obviously better, a VPN still isn’t perfect — it’s like drawing the curtains over your activities versus hanging out with the blinds open and lights on. That’s sufficient for the vast majority of us, but if you’re running a Soviet spy ring you probably need to look into more advanced options.
Which VPN to use?
Honestly, there are hundreds, and as long as the company is reputable and trustworthy, they all work about the same (unless you’re going to China, where the internet is more complicated in general). The VPN company can theoretically see any unencrypted traffic, so you don’t want to use a fly-by-night operation. I’ve used a few different ones:
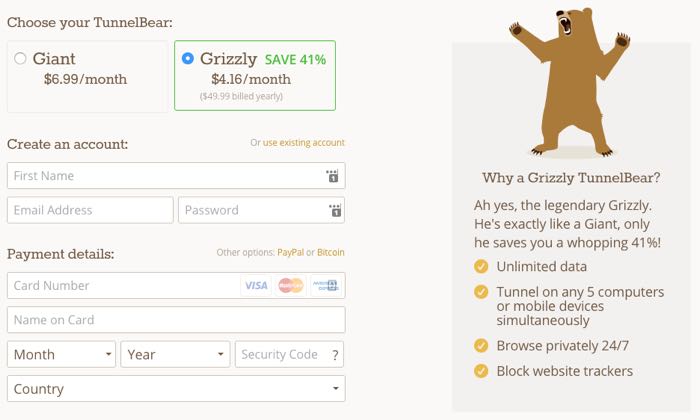
This is what I’m using currently. TunnelBear is cheap at less than $5 a month, it works on my computer and my phone, and I appreciate their commitment to the bear theme, which I find hilarious.
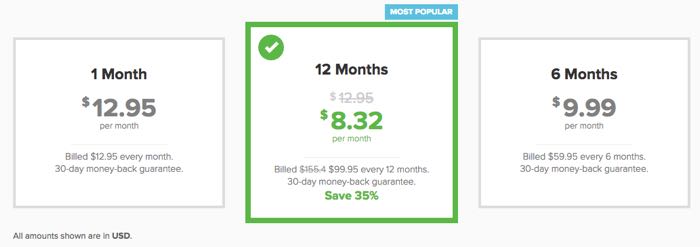
Last year I used ExpressVPN almost exclusively, and it worked really well. No problems in a variety of geographic locations, and the one time I did have a slight technical issue their customer service was fantastic. I would still be using them if I hadn’t decided to try out TunnelBear for science.
Astrill
Astrill worked best of any of the services we tested in China last year (but that situation is volatile). Their interface is a bit clunkier, but they have a “stealth mode” that worked brilliantly for getting to Twitter and YouTube in China.

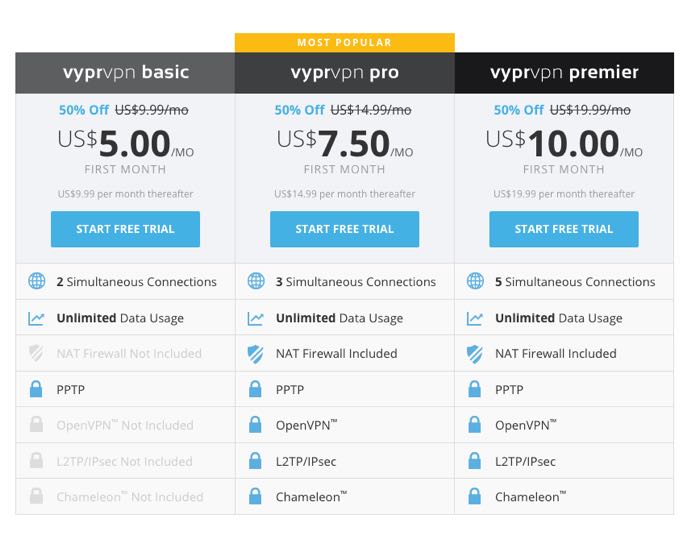
Vypr is a highly reputable service in China, and the one endorsed by my geek friends. It worked well, though the app was a bit fussier than Astrill. Ben ended up having to change servers pretty frequently, which was a little irritating, but it still worked well overall. I haven’t used it since though, as the app just isn’t as useable as the other three for everyday use.
So based on my experiences I would go with TunnelBear or ExpressVPN. If you’ve used others please share them in the comments!
Is it hard to set up a VPN?
Nope. With any of these services, you’ll install a program on your computer or phone. Once you connect to the internet, you then open the VPN app to create the network “shield.”
They all have great tutorials should you run into issues, but it generally takes less than five minutes to configure a VPN service.
The one caveat is that you’ll want to set them up before you’re traveling. There are many countries where you can’t access these websites to download a VPN, and it’s better to install these kinds of things from a reliable internet connection anyway.
Bottom line
If you’re accessing public WiFi, ever, you should be using a VPN.
The services aren’t that expensive, a VPN is easy to setup, and the extra protection is well worth it. You should also be using a password manager to create unique and complicated logins for individual sites (we use LastPass) as an added measure.
Do you use a VPN when you travel? Which one?




I think you are not safe when you use any open network whether it is in air plane or at some school. The best way to protect your data and privacy online is to connect through a VPN. If you are a mac user than this will help you alot
http://www.bestvpn.guide/best-vpn-for-mac/
I have a Netgear router (Nighthawk R7000) and it has built-in VPN functionality. With an app on my iPhone or Windows computer, I am able to establish a VPN connection that is secure/encrypted and don't have a monthly/annual fee to pay. It has worked on GoGo and in many other places. I have not tested it against internet filtering in countries like China, but it theoretically will work.
I travel to China a lot and have used all of the above services but many of them get blocked by the great firewall. The only service that I have found is consistently reliable around the world is ExpressVPN. More expensive than the other (cheaper if you buy annual plan for $99) but the service is exceptional. https://www.expressvpn.xyz?referrer_id=9129684&utm_campaign=referrals&utm_medium=copy_link&utm_source=referral_dashboard
Hi Tiffany,
Great article and insight into online security and VPNs. But I am surprised the focus of your article was on the protection of data rather than human life itself. Please review the following urls to discover what we can't see is hurting us. Wifi exposure is unhealthy, especially on planes:
http://www.naturalnews.com/042323_brain_cancer_risk_cell_phones_mobile_devices.html
http://bodyecology.com/articles/something_in_the_air_can_hurt_you.php
http://stopsmartmetersirvine.com/2012/02/19/dr-mercola-interviews-alasdair-philips-emfs-effect-on-health-what-the-research-is-showing-and-what-we-can-do-to-limit-radiation-exposure-from-wireless-devices/
Hi Tiffany,
Great article and insight into online security and VPNs. But I am surprised the focus of your article was on the protection of data rather than human life itself. Please review the following urls to discover what we can't see is hurting us. Wifi exposure is unhealthy, especially on planes:
http://www.naturalnews.com/042323_brain_cancer_risk_cell_phones_mobile_devices.html
http://bodyecology.com/articles/something_in_the_air_can_hurt_you.php
http://stopsmartmetersirvine.com/2012/02/19/dr-mercola-interviews-alasdair-philips-emfs-effect-on-health-what-the-research-is-showing-and-what-we-can-do-to-limit-radiation-exposure-from-wireless-devices/
Unfortunately some airlines block VPN use. Supposedly this is to prevent VOIP usage, which is harder to prevent if you're on a VPN.
And one more thing. How did the supposed hacker know which passenger it was who was the reporter? By hacking into the wifi system, all he would have seen is that someone's e-mails were a reporter's. There would have been no way to tell which of the people on the plane was the reporter.
Unless, of course, he didn't hack into the wifi system at all, but read the e-mails on the reporter's screen.
That USA Today story is suspect. The reporter says that the guy behind him tapped him on the shoulder and said he had read all the emails he sent and received during the flight, and "proved" it by summarizing some of their contents. OK, but it was the guy sitting behind him who had all this information about his e-mails. Was the reporter not the slightest bit curious as to whether the guy just read...
That USA Today story is suspect. The reporter says that the guy behind him tapped him on the shoulder and said he had read all the emails he sent and received during the flight, and "proved" it by summarizing some of their contents. OK, but it was the guy sitting behind him who had all this information about his e-mails. Was the reporter not the slightest bit curious as to whether the guy just read the e-mails over his shoulder, rather than by hacking into his wifi?
I can't believe how credulous this reporter is.
Other useful piece of software: an "https everywhere" extension, like the one in Chrome, to force all traffic to go to https if a website offers it. It even hides your google searches from your ISP and others on your network.
However, a VPN does not protect you fully, as the easiest attack on a network is trying to login to another computer on the same network if it has a weak password, or folders...
Other useful piece of software: an "https everywhere" extension, like the one in Chrome, to force all traffic to go to https if a website offers it. It even hides your google searches from your ISP and others on your network.
However, a VPN does not protect you fully, as the easiest attack on a network is trying to login to another computer on the same network if it has a weak password, or folders shared to the world, or an open bluetooth connection. A firewall helps, but doesn't protect against weak passwords!
Kudos Tiffany for one of the most useful and best blogs I've read. Easy to understand, yet still comprehensive for the novice. Also shout outs to the community for their complementary suggestions. Thank you.
Tiffany,
I am an IT professional and agree with your tips, well written and easy to understand.
A VPN is not always necessary but it does add a layer of security which never hurts.
Knowing that nothing over the internet is ever 100% safe, you can minimize your risks.
When traveling be careful when connecting to a wireless network. Make sure that the name of the access point you are connecting to is...
Tiffany,
I am an IT professional and agree with your tips, well written and easy to understand.
A VPN is not always necessary but it does add a layer of security which never hurts.
Knowing that nothing over the internet is ever 100% safe, you can minimize your risks.
When traveling be careful when connecting to a wireless network. Make sure that the name of the access point you are connecting to is truly the one the hotel or restaurant is providing. Many times there are a few to choose from and some of those could be someone trying to do something malicious. Another point to make is when you are on a guest wireless network like GoGo or one at a hotel you have access to the internet but you can not see or access other devices using the same WiFi. There is no Local Network connecting everyone. This is not always the case at some local Cafe using a home wifi router. Most using hardware designed for a business guest network will work this way. This is the first red flag which makes me not believe the USA today story.
What everyone should have:
1) Good AntiVirus Software (one which is updated often and protects against viruses, malware, rootkits, etc)
2) A firewall - While at home your router is also your firewall (probably) but when on the road it is important to have one installed. This prevents incoming traffic access to your computer unless it is something you have previously allowed.
3) VPN - While the firewall prevents things coming in, once they leave your computer it is outside your control. When you are on a secure website (https) the data is encrypted on your computer and decrypted at the other end. (and vice versa) A VPN does a similar thing except between you and the endpoint of the VPN. First do you trust the VPN company, who's to say they do not have a rouge employee steeling information? While a VPN is another layer of security I put this down in the list because like other users have said when browsing on secure sites you are transmitting this data encrypted. Same goes for logging into your bank, they are all https sites. But not everything is and it does help while traveling outside the country and you want to access something which is limited to the United States only. There are also different levels of encryption which I will not get into here.
People should also know that a VPN will slow things down. You are relying on the connection at the other end as well as the time it takes to encrypt/decrypt the data. Typically not bad but when you are on a very bad GoGo internet connection to begin with it could be like pulling teeth.
Which brings me to my last and most important point. I am fairly certain the USA Today Reporter made this story up. Without getting into too many technical details it really is too far fetched and too much of a coincidence IMO. I think he has watched too many movies and really has no clue how this all works. Yes Hacking/Hackers are real. Yes you need to be safe when using the internet. No it is not like the movies.
I agree with just about everything here, but I think you missed out on what I (and many in the industry) consider the best VPN client, Cloak.
http://thesweetsetup.com/apps/best-vpn-solution-ios-os-x/?utm_content=buffer6788e&utm_medium=social&utm_source=twitter.com&utm_campaign=buffer
Witopia is decent but their mobile setup is a bit more "manual". Currently using ExpressVPN - works great, starts up automatically when I boot up my PC (which is to say I like to ALWAYS be using VPN on any public network).
Anyone connecting to ANY public wifi really SHOULD be worried.
Are you sure about what you said in the beginning about the ISP being vulnerable? I always though https was secure all the way from your browser to the target site. It didn't matter if you were on public open wifi. Someone could see your encrypted data and maybe where it was going, but they wouldn't be able to read it.
PIA is a great one to use and you can also install it on your router if needed!
@sebastianschipr Don't use Hola! It has been shown to let others use your internet connection
I always use Hola VPN.. It is free on your PC/laptop.
Also has an iphone/adroid app for $4.99 a mounth or $49.99 a year.
hola.org/
Umm...which card do you use to pay for your VPN?
My work email on the laptop and mobile are automatically encrypted through an SSH tunnel to the Corp email servers - so I don't need to use a VPN.
For personal email, I use the Gmail app on iOS, so that's also automatically encrypted.
I only resort to using VPN to get to Netflix - and that's mostly not needed nowadays since they blew open all the countries I travel to!
But VPN of my choice is STRONGVPN from ReliableHosting.com
I use Private Internet Access and have always been happy with them.