One Mile at a Time brings you breaking travel news, reviews and strategies to maximize elite travel status.
Earn more miles, points and rewards with today’s top credit card offers.

Recent OMAAT Articles

- 31 mins ago
- Ben Schlappig

- 60 mins ago
- Ben Schlappig

- 2 hours ago
- Ben Schlappig

- 3 hours ago
- Ben Schlappig

- 14 hours ago
- Ben Schlappig

- 17 hours ago
- Ben Schlappig

- 19 hours ago
- Ben Schlappig

- 21 hours ago
- Ben Schlappig

- 23 hours ago
- Ben Schlappig

- 1 day ago
- Ben Schlappig
 Terms Apply. |
See Rates & Fees
Terms Apply. |
See Rates & Fees
- Earn 3x Points on Airfare
- Earn 3x Points on Hotels
- Earn 3x Points at Restaurants
- $95
TRAVEL REVIEW
Review: Singita Pamushana Lodge, Zimbabwe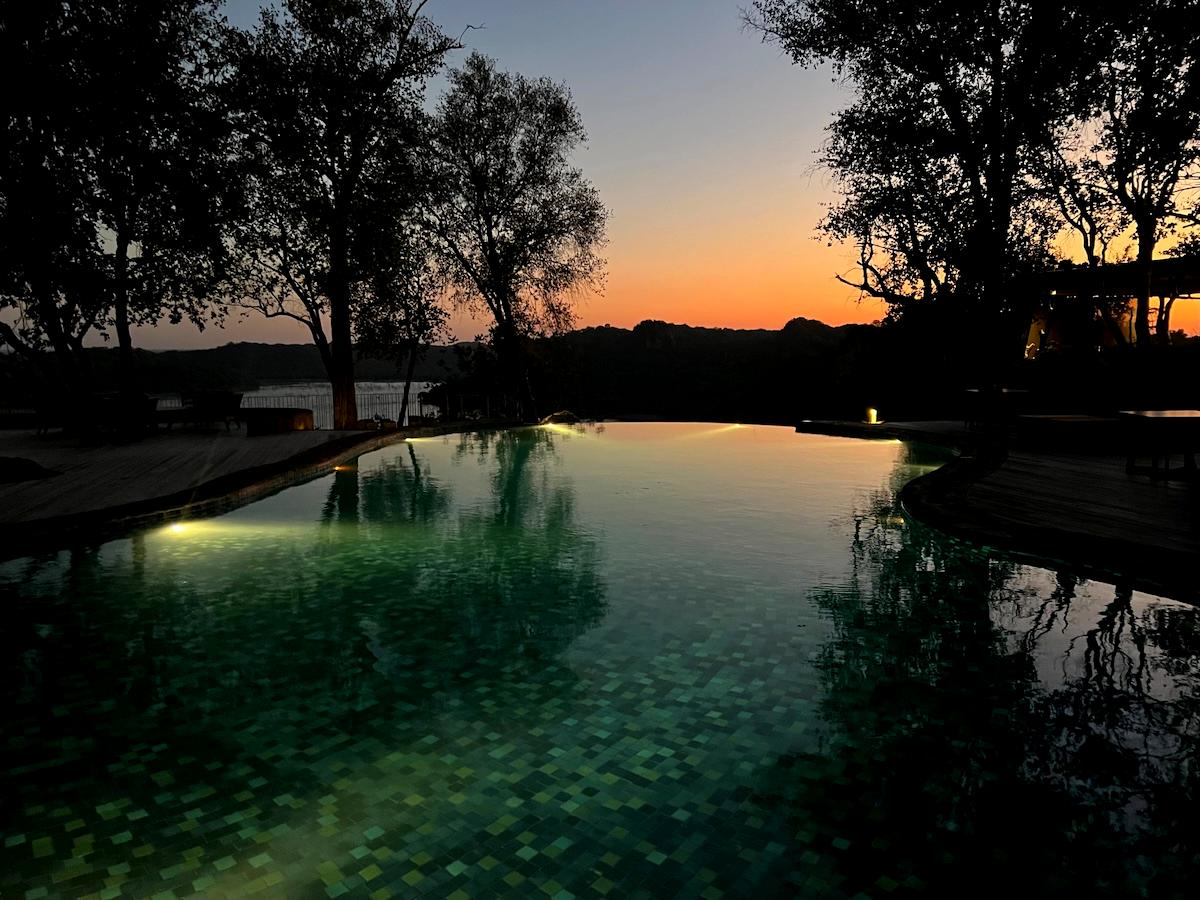
For our trip to Zimbabwe, our final destination was Singita Pamushana Lodge. Singita is known for offering some of Africa’s highest quality safari experiences. We took our first safari several years back, when we stayed at two of the brand’s South…

Latest Trip Reports

- March 27, 2024
- Ben Schlappig

- February 26, 2024
- Ben Schlappig
- February 3, 2024
- Ben Schlappig
The “Ask Lucky” page has been updated with a new “questions and answers” section.
Ask your miles and points questions, or share your tips to help other readers (while earning bonus status points).
See what's new Earn 75,000 bonus miles
Earn 75,000 bonus miles
 Earn 100,000 bonus points
Earn 100,000 bonus points
 Earn 80,000 Membership Rewards® Points
Earn 80,000 Membership Rewards® Points
 Earn 60,000 ThankYou points after qualifying purchases
Earn 60,000 ThankYou points after qualifying purchases

- 2 days ago
- Ben Schlappig
- Review: Corendon Amsterdam New-West, Marriott Tribute Portfolio
- Review: Corendon Amsterdam Schiphol Airport, Marriott Tribute Portfolio
- Review: Cheval Blanc St. Barts (Caribbean Palace Hotel)
- Review: Four Seasons Costa Rica At Peninsula Papagayo
- Review: Hotel Villa Fontaine Tokyo Haneda Airport (HND)
- Review: Seoul Incheon Airport Transit Hotel (ICN)
Check out our YouTube channel for easy tutorials and quick reviews, or join us for a Happy Hour/Livestream!

I’ve flown all of the major (and many minor) airlines, including every international first class cabin.
I write all my own content; no ghostwriters at OMAAT!
15 years (and counting) of daily blogging add up.